Physical Security

Track all your assets from the comfort of your desk
Talinda East Africa offers physical security your company's assets. We apply this by tagging each asset with a tag that has a special code. This solution comes with the barcode scanner, which takes the code form all the assets and keeps an accurate inventory.
The Inventory assists the Organization keep track of what the organization has, what is missing, what needs replenishing and what needs to be replaced.
This system allows regular updates on all repair and maintenance works of your assets. It is applicable in all industry types. Key assets which can be tagged include; furniture, electronics and machinery.

IP Surveillance Systems
IP surveillance is a digitized and networked version of closed-circuit television (CCTV). In an IP surveillance system, an IP camera records video footage and the resulting content is distributed over an IP (Internet protocol) network. Key features include;
- Improved search capability,
- Greater ease of use,
- Better quality images,
- No degradation of content over time,
- The ability to record and play simultaneously,
- Ability to compress content for improved storage,
- Improved ability for remote viewing and control meaning anyone on the network can potentially see video from any camera connected to the network
- Greater ease of distribution; An image of a crime suspect can be immediately distributed to officials.
- Easy ability to connect to email and other communications system to improve agility

Monitor and control all the movement in your premise
Biometrics access control is a security system that uses one part of the body for authentication and configured with the users unique parts like the eye, hand, fingerprint, etc. The information is then stored in the system. You are assured that only authorized personnel will access any restricted area in your premises. Bio-metrics can be applied in a wide range of sectors amongst them, Banking, Warehousing, Home, Education.
RFID Talinda uses electromagnetic fields to automatically identify and track tags attached to objects. The user will utilize a card which is configured with electromagnetic fields and programmed to open door locks. Whenever one requires to access an area with an RFID system, they simply swipe the card to enter. This improves security by ten-fold.
.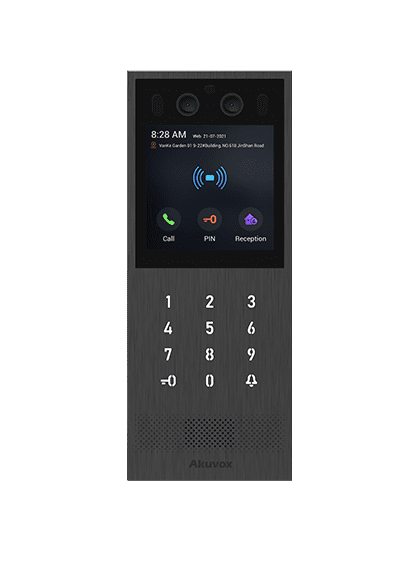
SIP Intercoms.
Our intercom solutions include different features including artificial intelligence, SIP, Android, cloud, security and other advanced technologies to deliver unparalleled intelligent access control experience in various vertical markets, from residential to commercial, healthcare to public safety.
The SIP intercom system allows tenants inside the building to communicate with guests outside the building. They also allow tenants to grant visitors access to the property through an "open door" button.
.
